Reddit member posted up that ATF activated his/her malware and asked for input. The results were really varied, but several stated “Yes, I get it” and others said “No, its not true”
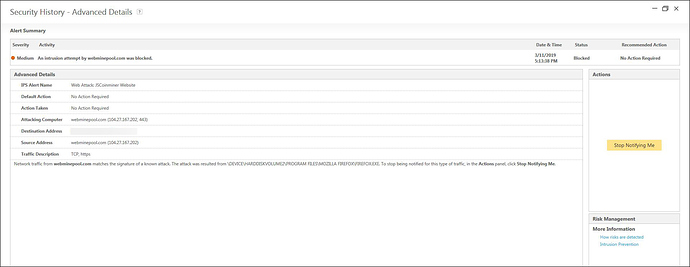
I saw it, tried it out and got the malware alert myself. I thought it was a false positive, I retried 10 separate attempts. It activated, indicating a malware code was alive.
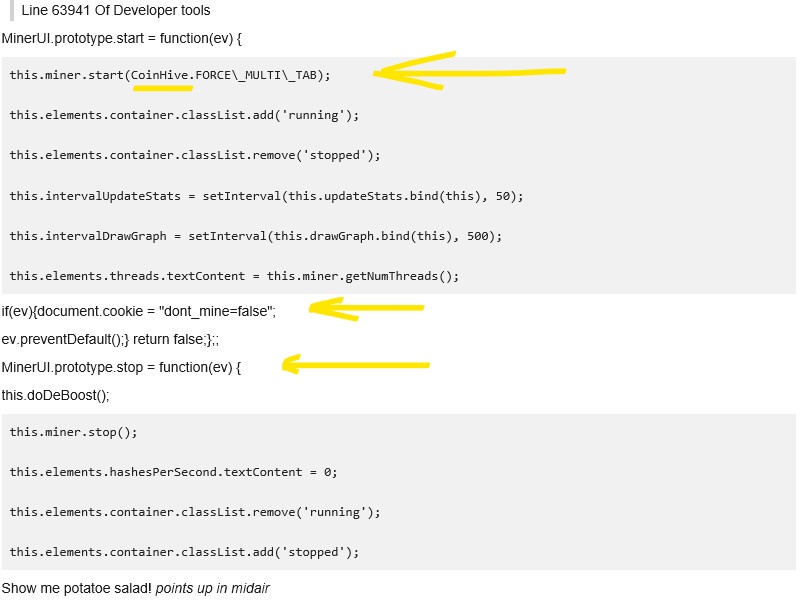
I F12’ed (pulled up developer tools of the site) and found a bitmoining code, down in the 6000 line’s which I have screenshot of and posted it. I then brought this to the thread (post on reddit) and the normal users/moderators started denying it, saying “trojans aren’t malware”, “it only activates if you click it”,
The reddit team defending trojans as “not being malware” falls into two categories.
• 1.They have no idea what malware is
• 2.They ARE aware, and part of the scam.
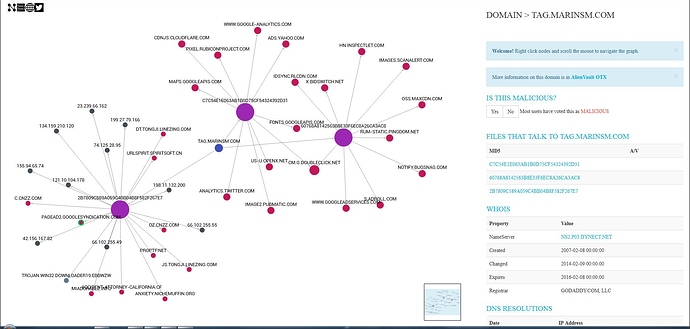
The code itself is bitmining, basically forcing computers to do problem solving in the form of a game to mine electronic currency. The dangers of it is that it can introduce viruses, but they can monetize from it.
Either the site manager was lying about an “inactive code” to the community,
or he was lying to the ATF team and has 2 codes in place.
-1. A decoy code that’s push start and just a store front
-2. A code in hiding that he’s monetizing personally from, that ATF isn’t aware of/ATF IS aware and getting a part of it.
Regardless, The site manager did he following
- he admitted to scamming people, (sarcastic or not),
- he delted the code rather quickly (deleted out of guilt? Deleted-because-someone-finally-noticed?) That’s not for me to figure out, but…
- started accusing me of “find something better to do”, “being mean”, “full of shit”.
…maybe this was TLDR as I thought, but that’s it in a short version.
But eh, what does this mean for an average user? To deactivate this decoy code,you had to “sign in” to turn it off. Sign in, being you had to pay/premium to log in and deactivate it.
Bitmining is a revenue generated, usually used in place of ads to take spot on a website and is usually in place of ads, not used in conjuction with them
. The unusual part of this is, the site manager/ATF team gets paid in three ways.
1= Site ads, automatically soon as you get on the site
2= Malware/Bitmining code= automatically as soon as you get on the site
3= Paying for premium to turn the decoy code off
An average user is basically paying the site to not have ADS AND to not have malware.
Take this for how you want to receive it, but…just be careful out there and make sure your computer has some kind of monitoring system, because the site manager reported that he used the same tactics that pirate bay users were doing (piracy sites) and “stopped doing it to avoid notice”, AND that credit card companies have denied working with him because they refused to operate on a malware-positive site.
(Malware = place you input credit card information for subscription is how you get your identify stolen)
Tread at your own risk and be safe.